12-12-2023
Exploring Virtual TOTP Tokens Experience
 We periodically get requests to provide testing units. In our usual practice, free samples aren't part of the equation. However, if you're eager to test the functionality, we've got some options that fully emulate the capabilities of our hardware tokens.
We periodically get requests to provide testing units. In our usual practice, free samples aren't part of the equation. However, if you're eager to test the functionality, we've got some options that fully emulate the capabilities of our hardware tokens.
user guides
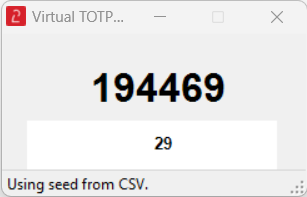
17-10-2023
Automating programmable token provisioning tasks with token2-config.exe
 The Token2 Configuration Tool (token2-config.exe) is a versatile and robust command-line utility specifically designed for configuring Token2 TOTP NFC Programmable tokens.
The Token2 Configuration Tool (token2-config.exe) is a versatile and robust command-line utility specifically designed for configuring Token2 TOTP NFC Programmable tokens.
user guides
18-08-2023
Introducing the New Python-Powered TOTP tool for Token2 FIDO2 Security Keys!
 Manage and use TOTP/HOTP codes via Python CLI script using a PC/SC device (USB NFC) or directly via USB. A cross-platform solution that works under Windows, macOS and Linux platforms.
Manage and use TOTP/HOTP codes via Python CLI script using a PC/SC device (USB NFC) or directly via USB. A cross-platform solution that works under Windows, macOS and Linux platforms.
Python-based tools are essential not only for their cross-platform compatibility, but also because their source-available nature allows experts/developers to examine the source code, ensuring transparency and minimizing the risk of hidden vulnerabilities or malicious elements. A GUI wrapper for the script is also available.
product updates
23-06-2023
Token2 PIN+ Series: Enhanced FIDO2 Security Keys
 Token2 is excited to announce the start of the mass production of their revolutionary PIN+ series, a line of FIDO2 Security keys. These security keys feature advanced PIN complexity rules that set a new standard for security. The firmware development for the PIN+ series is now complete, and the company is currently making preparations for mass production.
Token2 is excited to announce the start of the mass production of their revolutionary PIN+ series, a line of FIDO2 Security keys. These security keys feature advanced PIN complexity rules that set a new standard for security. The firmware development for the PIN+ series is now complete, and the company is currently making preparations for mass production.
product updates
08-06-2023
Azure AD Now Supports FIDO2 Security Keys on Safari on iOS
 In a significant development for iOS users, Microsoft Azure Active Directory (AD) has expanded its support for FIDO2 security keys on the Safari browser. This advancement is a crucial step towards enhancing security and usability on Apple's mobile devices, ensuring seamless authentication experiences for Azure AD users. With FIDO2 security keys, users can now enjoy passwordless access to their Azure AD accounts, boosting convenience and significantly reducing the risk of password-related attacks. Let's dive deeper into this exciting development and explore the benefits it brings to iOS users.
In a significant development for iOS users, Microsoft Azure Active Directory (AD) has expanded its support for FIDO2 security keys on the Safari browser. This advancement is a crucial step towards enhancing security and usability on Apple's mobile devices, ensuring seamless authentication experiences for Azure AD users. With FIDO2 security keys, users can now enjoy passwordless access to their Azure AD accounts, boosting convenience and significantly reducing the risk of password-related attacks. Let's dive deeper into this exciting development and explore the benefits it brings to iOS users.
updates
15-05-2023
Azure AD Authentication methods policy migration
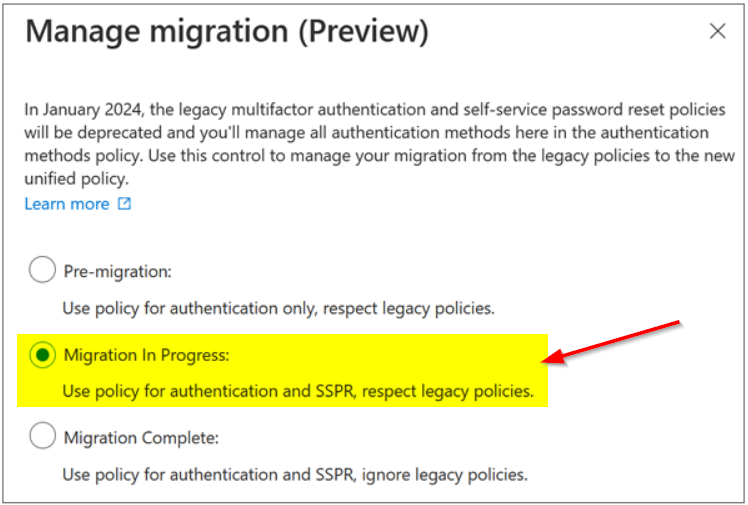 In an effort to enhance security and streamline administration, Microsoft introduced the Authentication methods policy for Azure AD. This policy allows administrators to manage the MFA and SSPR settings from a single location, simplifying the overall user experience. However, it's important to note that the migration process has a limitation when it comes to hardware OATH tokens.
In an effort to enhance security and streamline administration, Microsoft introduced the Authentication methods policy for Azure AD. This policy allows administrators to manage the MFA and SSPR settings from a single location, simplifying the overall user experience. However, it's important to note that the migration process has a limitation when it comes to hardware OATH tokens.
integration guides
05-05-2023
Molto2 Receives "Certified Product" Badge from Independent Third-Party Assessment by SySS GmbH
 At our company, we believe in delivering safe and secure products to our customers. That's why we engaged SySS GmbH, an independent third-party security company, to conduct a thorough security assessment of our product, Molto2. We are proud to announce that Molto2 has passed this assessment with flying colors and has received a "Certified Product" badge from SySS GmbH.
At our company, we believe in delivering safe and secure products to our customers. That's why we engaged SySS GmbH, an independent third-party security company, to conduct a thorough security assessment of our product, Molto2. We are proud to announce that Molto2 has passed this assessment with flying colors and has received a "Certified Product" badge from SySS GmbH.
product updates
21-04-2023
Introducing Token2 FIDO2 PIN+: The Security Key That Enforces Strong PIN Complexity
 We are excited to announce the upcoming launch of our latest product variation, the Token2 FIDO2 PIN+. The PIN+ series is a new variation of our existing security keys that deviates from the FIDO2 standards to provide stronger PIN complexity enforcement.
We are excited to announce the upcoming launch of our latest product variation, the Token2 FIDO2 PIN+. The PIN+ series is a new variation of our existing security keys that deviates from the FIDO2 standards to provide stronger PIN complexity enforcement.
product updates
07-04-2023
Enhancing Security with the Token2 Molto-2 Lock Screen Feature
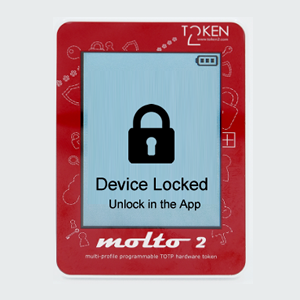 The Token2 Molto-2 is a popular multiprofile hardware token used for two-factor authentication, providing an additional layer of security for various online services and systems. With the latest version of the device, a new feature has been added that allows users to lock the device screen for added security.
The Token2 Molto-2 is a popular multiprofile hardware token used for two-factor authentication, providing an additional layer of security for various online services and systems. With the latest version of the device, a new feature has been added that allows users to lock the device screen for added security.
product updates
22-03-2023
iOS Mail or Outlook App for Office 365 Users with Passwordless Authentication
 As more and more organizations adopt a passwordless method of authentication, users are faced with the challenge of configuring their email accounts on their mobile devices.
As more and more organizations adopt a passwordless method of authentication, users are faced with the challenge of configuring their email accounts on their mobile devices.
guides
20-03-2023
Unlocking the Benefits of Azure Passwordless with FIDO2 Keys
 We understand that some of our customers have questions and concerns about migrating to Azure Passwordless with FIDO2 keys. With this blog post, we aim to address and clarify some of the common queries that may arise regarding the technology.
We understand that some of our customers have questions and concerns about migrating to Azure Passwordless with FIDO2 keys. With this blog post, we aim to address and clarify some of the common queries that may arise regarding the technology.
review
30-01-2023
Top myths about FIDO2 security keys and Passwordless access
 We have been getting quite a lot of questions about the security level of FIDO keys, in the light of some recent news and research papers covering potential vulnerabilities of both the protocol stack itself and the hardware of certain implementations.
We have been getting quite a lot of questions about the security level of FIDO keys, in the light of some recent news and research papers covering potential vulnerabilities of both the protocol stack itself and the hardware of certain implementations.
review
03-01-2023
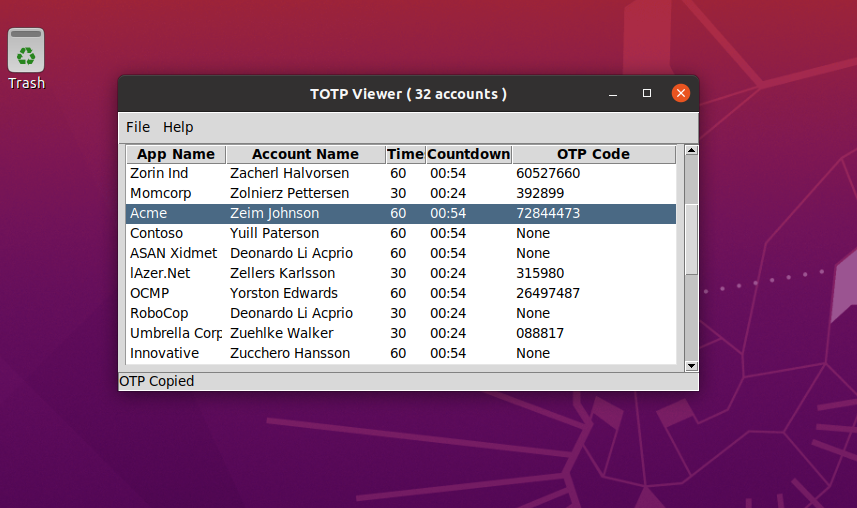
molto2.py - Molto2 USB Config tool
 molto2.py is a solution developed by Token2 to program and configure the Molto2v2 TOTP hardware tokens using pyscard python library. It is fully cross-platform and works under Linux, macOS and Windows operating systems.
molto2.py is a solution developed by Token2 to program and configure the Molto2v2 TOTP hardware tokens using pyscard python library. It is fully cross-platform and works under Linux, macOS and Windows operating systems.
product updates
15-12-2022
Introducing Passwordless Login for Our Website!
 At Token2, we are always looking for ways to improve the user experience and make it as convenient and secure as possible. That's why we are excited to announce the addition of a passwordless login option for our website.
At Token2, we are always looking for ways to improve the user experience and make it as convenient and secure as possible. That's why we are excited to announce the addition of a passwordless login option for our website.
website updates
05-12-2022
Provisioning Token2 TOTP programmable tokens - a universal guide
 We have a lot of integration guides describing the process of enrolling our programmable tokens with different systems, such as Google, Microsoft, Facebook and many others.
We have a lot of integration guides describing the process of enrolling our programmable tokens with different systems, such as Google, Microsoft, Facebook and many others.
integration guides
17-08-2022
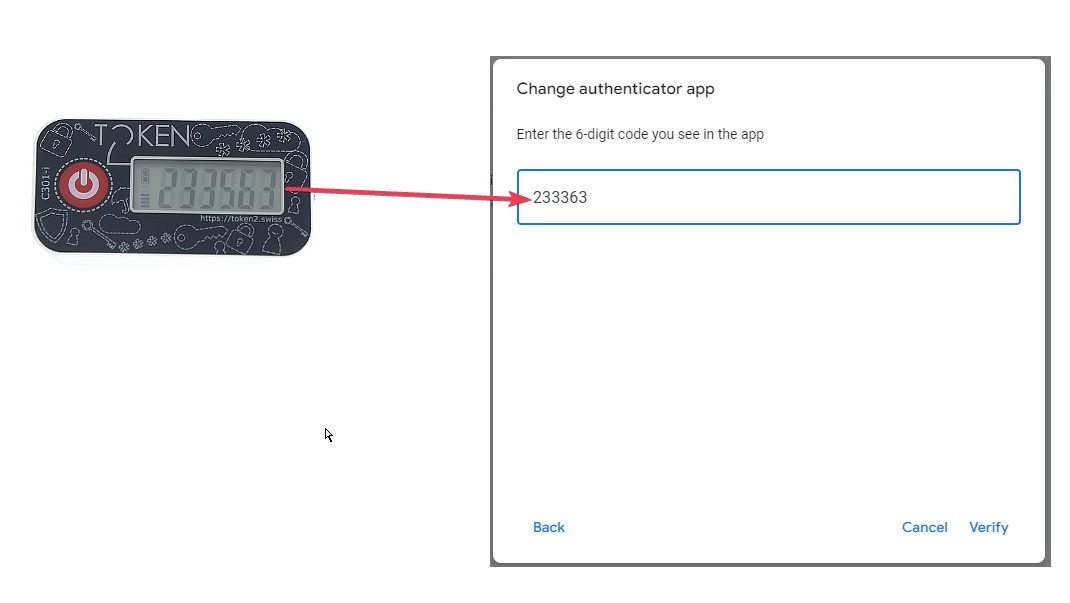
Using programmable hardware tokens with Azure AD B2C
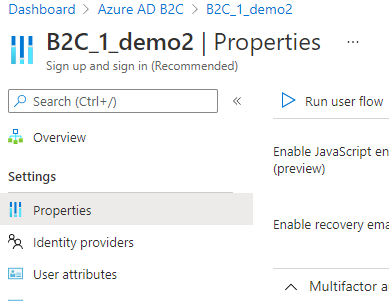 On August 16th, 2022, Microsoft announced TOTP-based MFA for Azure AD B2C as generally available. The name used for this authentication method is "OATH software tokens", which is another name for TOTP authentication apps like Google Authenticator or Microsoft Authenticator.
On August 16th, 2022, Microsoft announced TOTP-based MFA for Azure AD B2C as generally available. The name used for this authentication method is "OATH software tokens", which is another name for TOTP authentication apps like Google Authenticator or Microsoft Authenticator.
integration guides
09-06-2022
Python version of the NFC Burner app - token2_config.py
 We have been getting many requests from the customers asking to make the NFC Burner tools available under macOS and Linux.
We have been getting many requests from the customers asking to make the NFC Burner tools available under macOS and Linux.
product updates
27-01-2022
PolKit vulnerability (CVE-2021-4034)
 A memory corruption vulnerability (CVE-2021-4034) in PolKit, a component used in major Linux distributions and some Unix-like operating systems, can be easily exploited by local unprivileged users to gain full root privileges.
A memory corruption vulnerability (CVE-2021-4034) in PolKit, a component used in major Linux distributions and some Unix-like operating systems, can be easily exploited by local unprivileged users to gain full root privileges.
product updates
23-12-2021
Using classic tokens for Native OTP Authentication with NetScaler
 Citrix ADC(NetScaler) supports one-time passwords (OTPs) without having to use a third-party server. One-time password is a highly secure option for authenticating to secure servers, as the number or passcode generated is random.
Citrix ADC(NetScaler) supports one-time passwords (OTPs) without having to use a third-party server. One-time password is a highly secure option for authenticating to secure servers, as the number or passcode generated is random.
integration guides
15-12-2021
Log4Shell (CVE-2021-44228)
 Token2 is aware of the RCE vulnerability in the Apache Log4j , classified by the Apache security team as a critical severity issue (CVE-2021-44228).
Token2 is aware of the RCE vulnerability in the Apache Log4j , classified by the Apache security team as a critical severity issue (CVE-2021-44228).
product informaion
Subscribe to our mailing list
Want to keep up-to-date with the latest Token2 news, projects and events? Join our mailing list!