16-11-2021
TOTPRadius : Azure AD Proxy mode
 The LDAP proxy mode of TOTPRadius was introduced as a workaround for implementing 2FA access for systems without native support for multiple authentication sources. This works perfectly fine for organizations with full on-premises or hybrid Active Directory implementations where domain controllers can be accessed over the local network directly using LDAP protocol. But we are discovering more and more organizations moving to full cloud Azure AD implementation while keeping some services, such as VPN, on-premises. As the LDAP interface of Azure AD is not accessible directly, it was not possible to configure TOTPRadius to use Azure AD as its authentication source.
The LDAP proxy mode of TOTPRadius was introduced as a workaround for implementing 2FA access for systems without native support for multiple authentication sources. This works perfectly fine for organizations with full on-premises or hybrid Active Directory implementations where domain controllers can be accessed over the local network directly using LDAP protocol. But we are discovering more and more organizations moving to full cloud Azure AD implementation while keeping some services, such as VPN, on-premises. As the LDAP interface of Azure AD is not accessible directly, it was not possible to configure TOTPRadius to use Azure AD as its authentication source.
product updates
16-11-2021
The Network Policy Server (NPS) extension for Azure. Verification methods.
 The Network Policy Server (NPS) extension for Azure Multi-Factor-Authentication (Azure MFA) provides a simple way to add cloud-based MFA capabilities to your authentication infrastructure using your existing NPS servers.
The Network Policy Server (NPS) extension for Azure Multi-Factor-Authentication (Azure MFA) provides a simple way to add cloud-based MFA capabilities to your authentication infrastructure using your existing NPS servers.
integration guides
20-10-2021
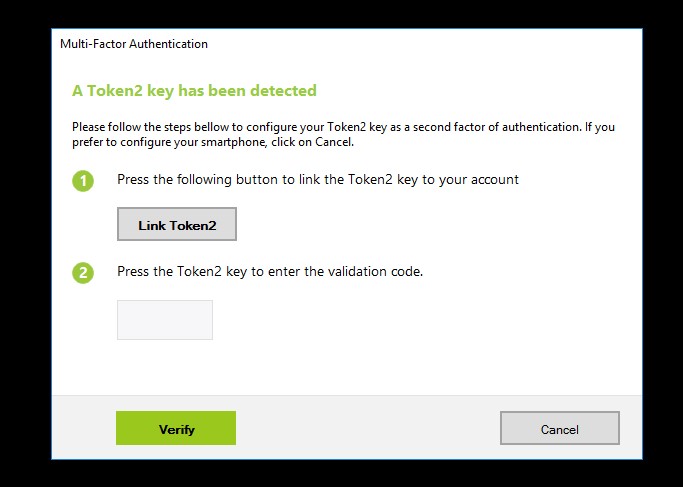
Securing Salesforce with Token2 Security keys or TOTP Tokens
 To protect your Salesforce account and data from unauthorized access, your org can require an extra layer of security when you log in.
To protect your Salesforce account and data from unauthorized access, your org can require an extra layer of security when you log in.
integration guides
16-09-2021
How to transfer TOTP profiles from Authy to a Token2 hardware token
 Authy remains one of the most popular TOTP application used for 2FA due to its user-friendly features, such as centralized backup. As this feature is based on phone numbers (Authy uses your mobile phone number to identify or reset your account), which may be vulnerable to sim-swap attacks, some users may want to migrate from Authy to hardware tokens. Or, alternatively, users may need to clone/backup their existing TOTP profiles to hardware tokens.
Authy remains one of the most popular TOTP application used for 2FA due to its user-friendly features, such as centralized backup. As this feature is based on phone numbers (Authy uses your mobile phone number to identify or reset your account), which may be vulnerable to sim-swap attacks, some users may want to migrate from Authy to hardware tokens. Or, alternatively, users may need to clone/backup their existing TOTP profiles to hardware tokens.
tools
16-09-2021
Hardware tokens for PPTP VPN on Windows Server using TOTPRadius
 TOTPRadius can be used if you need to have hardware tokens as the second factor for two-factor authentication with Windows Server based PPTP VPN. You can enroll the same tokens as with Azure MFA, so your users can use the same hardware token for both Office 365 and VPN Access. The guide below explains how you can integrate TOTPRadius with Windows Server to achieve this.
TOTPRadius can be used if you need to have hardware tokens as the second factor for two-factor authentication with Windows Server based PPTP VPN. You can enroll the same tokens as with Azure MFA, so your users can use the same hardware token for both Office 365 and VPN Access. The guide below explains how you can integrate TOTPRadius with Windows Server to achieve this.
integration guides
15-07-2021
How to transfer TOTP profiles from Google Authenticator to a Token2 hardware token
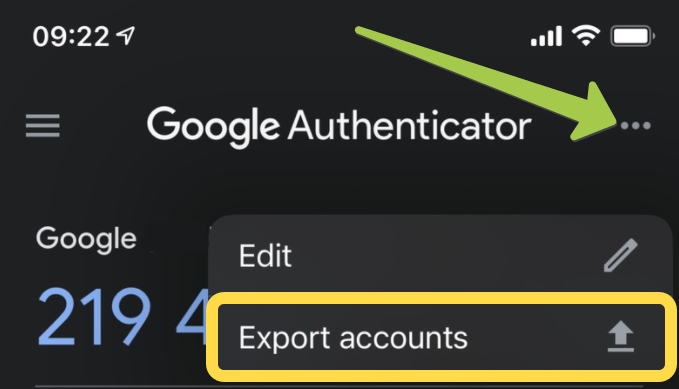 Presenting Token2 Migration toolset, a tool to convert the Google Authenticator's export file to formats possible to be uploaded or burnt to Token2 hardware tokens.
Presenting Token2 Migration toolset, a tool to convert the Google Authenticator's export file to formats possible to be uploaded or burnt to Token2 hardware tokens.
tools
29-06-2021
Molto-2 v2, the second revision of our most popular multi-profile TOTP hardware token
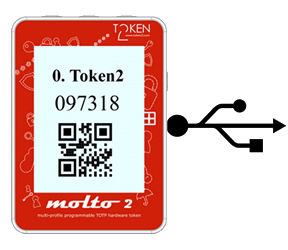 A new version of our popular Molto-2 token is coming.
A new version of our popular Molto-2 token is coming.
product updates
05-03-2021
Token2 TOTPRadius v0.2.5 has been released
 Starting from v0.2.5 TOTPRadius provides new ways of connecting to your corporate VPN systems based on L2TP, such as Meraki Client VPN or Fortinet VPN . The new web-based VPN portal allows logging in using additional methods, such as FIDO Security keys, both in Passwodless mode (if FIDO2 keys are used) and using the keys as the second factor (allowing to use legacy U2F FIDO hardware), as well as Azure AD SSO via OAuth2 protocol.
Starting from v0.2.5 TOTPRadius provides new ways of connecting to your corporate VPN systems based on L2TP, such as Meraki Client VPN or Fortinet VPN . The new web-based VPN portal allows logging in using additional methods, such as FIDO Security keys, both in Passwodless mode (if FIDO2 keys are used) and using the keys as the second factor (allowing to use legacy U2F FIDO hardware), as well as Azure AD SSO via OAuth2 protocol.
product updates
02-03-2021
Azure AD - Protecting user accounts with FIDO2 keys without MFA requirement
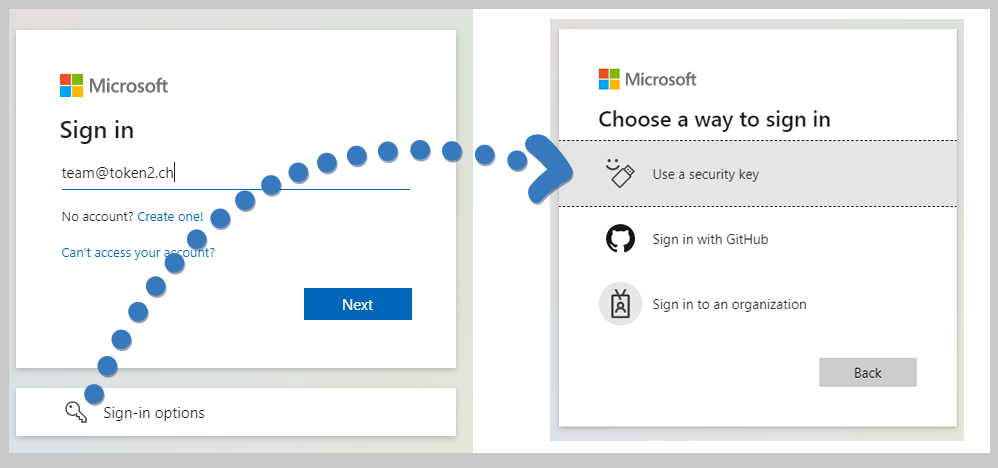 FIDO2 keys as a security method is available with Microsoft Azure AD for already a couple of years now. Being the most secure access method available for Office 365 user access, enrolling FIDO2 security keys had a requirement of MFA to be configured for the users, which made it useless for use cases where users do not have (or do not want) to use multiple devices to log in. This has finally changed!
FIDO2 keys as a security method is available with Microsoft Azure AD for already a couple of years now. Being the most secure access method available for Office 365 user access, enrolling FIDO2 security keys had a requirement of MFA to be configured for the users, which made it useless for use cases where users do not have (or do not want) to use multiple devices to log in. This has finally changed!
integration guides
11-02-2021
UserLock v11 released, now with Token2 Security keys native support
 UserLock now supports the use of Token2 Security keys as a second factor authentication.
UserLock now supports the use of Token2 Security keys as a second factor authentication.
integration guides
08-02-2021
Programmable hardware tokens for Office 365 - is self-service possible?
 With NFC tokens, the provisioning is done by the IT person equipped with software and hardware that allows burning seeds onto programmable hardware tokens (i.e. an Android device with NFC, iPhone 8 or newer for “-i” models etc.). . However, we have many customers asking if this process can be done by end-users in a fully autonomous manner.
With NFC tokens, the provisioning is done by the IT person equipped with software and hardware that allows burning seeds onto programmable hardware tokens (i.e. an Android device with NFC, iPhone 8 or newer for “-i” models etc.). . However, we have many customers asking if this process can be done by end-users in a fully autonomous manner.
integration guides
28-11-2020
Connecting to VPN with FIDO Security keys using TOTPRadius FIDO-VPN Interface
 Multi-factor authentication for VPN systems, such as Meraki Client VPN or Fortinet VPN will be possible using FIDO Security keys, both FIDO2 and U2F.
Multi-factor authentication for VPN systems, such as Meraki Client VPN or Fortinet VPN will be possible using FIDO Security keys, both FIDO2 and U2F.
product updates totpradius
30-10-2020
Two Factor Authentication in VMware Horizon View with TOTPRadius
 VMware Horizon View enables you to access a virtual desktop from anywhere, anytime.
VMware Horizon View enables you to access a virtual desktop from anywhere, anytime.
integration guides
25-10-2020
Hardware tokens for PayPal Two-Factor Authentication
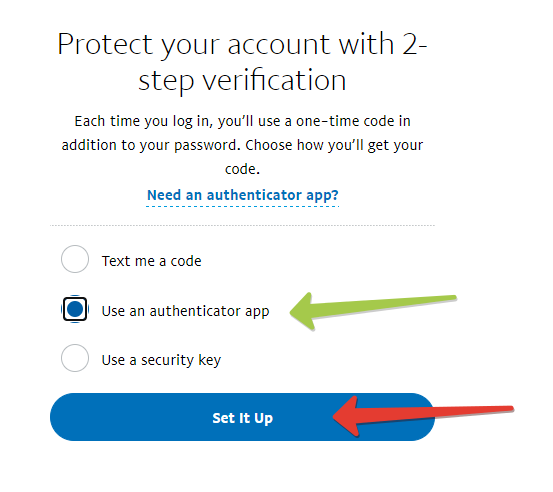 Until around 2019, PayPal offered two-factor authentication security via SMS only. And while SMS 2FA is better than no 2FA at all, users wanted better protection. Now you can secure your PayPal account with a hardware token, by using Token2 programmable hardware token as a drop-in replacement of mobile authenticator apps.
Until around 2019, PayPal offered two-factor authentication security via SMS only. And while SMS 2FA is better than no 2FA at all, users wanted better protection. Now you can secure your PayPal account with a hardware token, by using Token2 programmable hardware token as a drop-in replacement of mobile authenticator apps.
integration guides
15-09-2020
Hardware tokens for Zoom Two-Factor Authentication

In a recent blog post, Zoom announced the launch of two-factor authentication for all users. With this feature, Zoom attempts to protect the users from potential security breaches.
integration guides
03-09-2020
Molto-2 is coming
 About a year ago, we released Token2 Molto-1, the world's first programmable multi-profile hardware token. While Molto-1 is still the only solution of its kind currently available on the market, we will be soon releasing a new variation of a multi-profile hardware token, in a different form-factor and with a different set of features available.
About a year ago, we released Token2 Molto-1, the world's first programmable multi-profile hardware token. While Molto-1 is still the only solution of its kind currently available on the market, we will be soon releasing a new variation of a multi-profile hardware token, in a different form-factor and with a different set of features available.
new product
03-09-2020
Provisioning programmable hardware tokens for Office 365 accounts remotely
 Many customers are asking about the best practices on provisioning the programmable hardware tokens in situations when end-users are working remotely and cannot burn the tokens themselves, so IT support has to take care of the burning process. To remind, using programmable hardware tokens is the only way to have a hardware token for MFA if the user is not licensed for Azure AD Premium.
Many customers are asking about the best practices on provisioning the programmable hardware tokens in situations when end-users are working remotely and cannot burn the tokens themselves, so IT support has to take care of the burning process. To remind, using programmable hardware tokens is the only way to have a hardware token for MFA if the user is not licensed for Azure AD Premium.
integration guides
31-08-2020
How to bulk activate OATH hardware tokens with Azure MFA
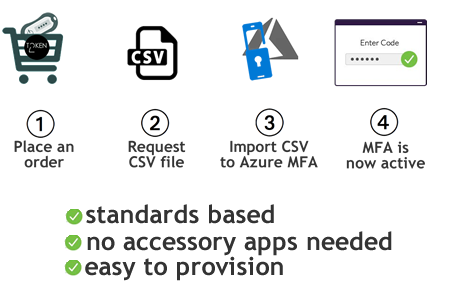 Token2 has developed a solution to automate the activation of imported hardware tokens with Azure MFA.
Token2 has developed a solution to automate the activation of imported hardware tokens with Azure MFA.
integration guides
07-08-2020
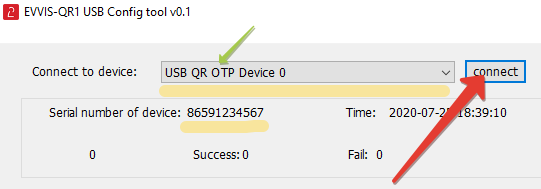
EVVIS-QR1 USB Programmable TOTP hardware token
 Today, we are presenting a new type of TOTP hardware tokens — USB Programmable token that displays the OTP value as a QR code and also can send the current OTP value over USB as a part of its HID emulation feature.
Today, we are presenting a new type of TOTP hardware tokens — USB Programmable token that displays the OTP value as a QR code and also can send the current OTP value over USB as a part of its HID emulation feature.
new product
17-07-2020
New integration guides published: Nextcloud and Fortinet
 We have published integration guides for two popular products, Nextcloud and Fortinet
We have published integration guides for two popular products, Nextcloud and Fortinet
integration guides
Subscribe to our mailing list
Want to keep up-to-date with the latest Token2 news, projects and events? Join our mailing list!